How to Prevent a Data Breach: A Complete Guide
If you’ve ever thought that your company is too small to become a target of cyber threats, it’s not exactly true.
Because in reality, most data breaches don’t happen in huge corporations with massive budgets. They happen to businesses that are smaller, and, most importantly, businesses that simply don’t expect to become a target.
A data breach doesn’t usually feel like some dramatic moment from a movie, where a hacker in a hoodie is typing furiously and breaking into a system. No, it's often quiet, subtle, and almost invisible. For example, it could be something as simple as a weak password or just one careless click.
In this article, we’re going to talk about data breaches properly, so you get a clear understanding of how it all actually works. Our guide is practical and filled with tips you can actually apply. Whether you’re running a business, managing client data in a corporation, or just trying to be more mindful with your own personal information.
What Is Data Breach Prevention?
Data breach prevention is about reducing the chances that sensitive information gets stolen, accessed, or exposed without proper permission. Sensitive information can be anything that carries important data that could be used improperly. For example:
- customer data
- phone numbers
- emails
- bank details
- internal documents
- login credentials
- employee salary information, and so on.
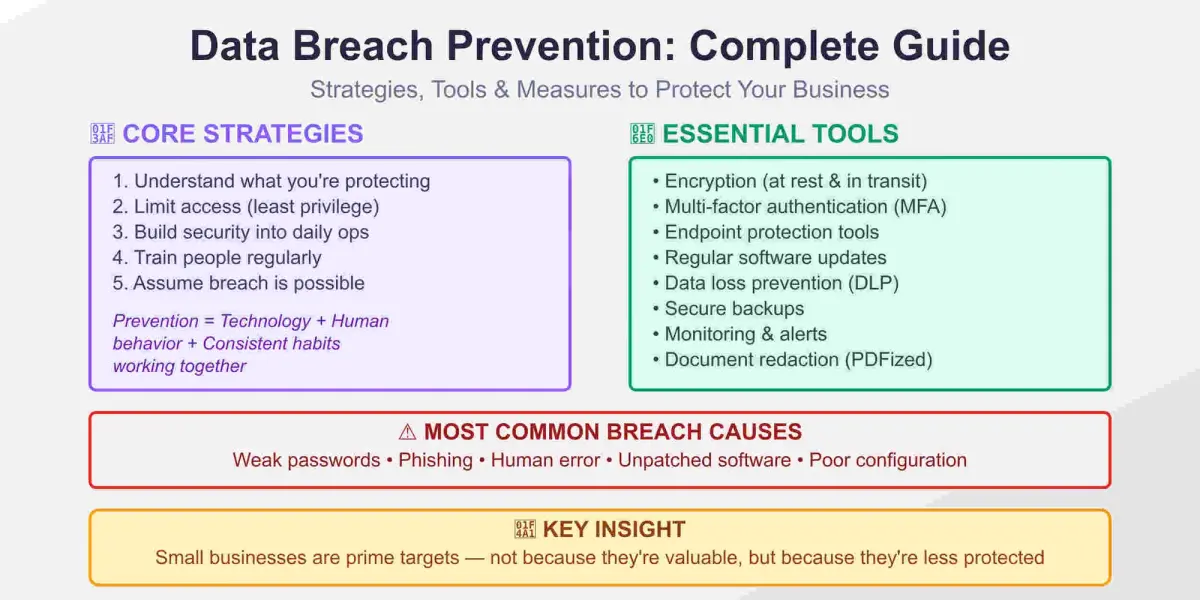
An important thing to understand is that prevention isn’t only about technology. It’s about human behavior, habits, and awareness working together as one system. To make it more relatable, think about your apartment. When you lock it, you don’t just lock the door, you also close the windows. The same logic applies in a digital environment. The goal isn’t to become 100% invincible, because that’s simply impossible. The goal is to make breaches significantly harder and much less likely.
Data Breach Prevention Strategies
Before you start using specific tools and methods, you need to build a strong strategy. Here’s how to do it:
Understand what you're protecting
You can’t protect what you don’t fully understand. Start with a simple question: ‘What data do we actually have?’ You need to clearly understand what data you have, for example PII, where your data is stored, who has access to it, and how it is shared between employees, clients, and other involved parties. This kind of clarity often reveals surprising gaps in your system.
Limit access
Not everyone needs access to everything. This is called ‘the principle of least privilege’, but in simple terms, it means giving people access only to what they actually need and nothing more. Remember that only one account with too much access can open everything.
Build security into daily operations
Security shouldn’t feel like a separate task. It should be part of your daily routine. For example:
- using password managers
- secure file-sharing tools
- automatic system updates
- avoiding random or suspicious links
When security is built into the system, people follow it naturally.
Train people
Most breaches happen because of human error. The reason isn’t that people are careless, but because they are tired, busy, or overloaded. Training should include:
- how to recognize phishing emails
- why password reuse is dangerous
- what to do if something feels suspicious
These training sessions should be short, practical, and regular.
Assume a breach is possible
This might sound uncomfortable, but it can completely shift your mindset. When you think: ‘What if this gets breached?’, – you naturally store less unnecessary data, encrypt more information, and monitor your systems better. You can also follow proven data security best practices to strengthen your overall system.
Data Breach Prevention Measures and Tools
Now let’s move to more concrete steps – tools and measures that actually make a difference.
Encryption
Encryption protects both:
- stored data
- data being transmitted
Even if someone gains access to encrypted data, it becomes useless without the key.
Multi-Factor Authentication (MFA)
This is one of the simplest and most effective protection methods. Even if a password is stolen, multi-factor authentication adds an extra layer of security. It can include:
- SMS codes
- authentication apps
- biometric verification
And it significantly reduces risks.
Endpoint protection
Every device connected to your system is a potential entry point. Endpoint protection tools can:
- detect malware
- block threats in real time
- monitor suspicious activity continuously
Regular software updates
This might sound boring but it’s critical. Many breaches happen because of outdated software. Updates help fix vulnerabilities and make it much harder for attackers to access your system.
Data loss prevention (DLP) tools
These tools monitor and control how data is used and shared. They can prevent sensitive data from being sent externally, block unauthorized transfers, detect unusual downloads and activity
Secure backups
Backups don’t prevent breaches but they significantly reduce potential damage. They allow you to restore data and avoid paying hackers..
Monitoring and alerts
Good monitoring systems detect unusual activity, send alerts, and help you respond quickly to threats.
Data Breach Prevention Tips
Now let’s go through some practical habits that really matter when it comes to preventing data breaches.
- Use a password manager and stop reusing passwords
- Turn on multi-factor authentication everywhere possible
- Avoid public Wi-Fi when handling sensitive tasks
- Regularly review who has access to your systems
- Don’t store data “just in case”
- Always verify unexpected requests, even if they look normal
- Keep personal and business accounts separate
And one more important thing: slow down before clicking a link as most breaches rely on urgency. The more rushed and unfocused you are, the easier it is to make a mistake that can lead to serious problems.
If you’re looking for structured resources and practical tools to manage and protect your data, some online platforms can be especially useful. One of the key features is document redaction. Properly redacted documents are truly secure because sensitive information cannot be copied or recovered.
Unlike simple black boxes that only visually hide data, tools like PDFized completely remove sensitive information completely, and that’s a very important difference when it comes to real data protection.
How to Prevent a Data Breach in a Small Business
Small businesses are actually one of the most common targets. It’s not because they’re highly valuable individually but because they are often less protected. Here’s how to approach it effectively:
Start with the basics
You don’t need enterprise-level tools. Focus on strong passwords, secure Wi-Fi, and regular updates.
Use cloud services wisely
Good cloud providers offer built-in security. But you still need to configure settings properly and manage access.
Outsource when needed
You don’t have to do everything yourself. Managed IT services can monitor your systems and respond to threats.
Create a simple incident plan
Even a basic plan can make a big difference. You should clearly understand who to contact, which systems are affected, and how to inform clients. This helps you avoid panic and reduces the risk of making critical mistakes.
What to Do After a Data Breach
Even the best preventive systems reduce risk, but they don’t eliminate it completely. Here’s what you should do if a breach actually occurs:
Control the breach
Immediately disconnect affected systems and stop data flow if possible.
Assess the damage
Understand what data was exposed, how it happened, how long it went unnoticed.
Notify relevant parties
Depending on your industry, there are different parties that must be notified. This may include customers, partners, regulatory organizations and authorities. Transparency is key here.
Fix the vulnerability
Don’t just deal with the damage, understand the cause. Was it a human error or a weak system configuration? You need to eliminate the vulnerability after the breach is contained.
Learn and improve
This is the most important part. A breach, while stressful, can become a turning point if you handle it correctly and learn more about sensitive data protection from it.
Comparison Table: Most Popular Data Breaches
To understand how breaches actually happen, it helps to look at real examples.
| Company | Year | Cause of breach | Data exposed | Impact |
|---|---|---|---|---|
| Yahoo | 2013 | Weak security & outdated systems | 3 billion accounts | Massive reputational damage |
| Equifax | 2017 | Unpatched vulnerability | 147 million records | $700M+ in settlements |
| 2019 | Misconfigured databases | 540 million user records | Trust and privacy concerns | |
| Marriott | 2018 | Unauthorized access | 500 million guest records | Long-term brand impact |
| 2021 | Scraped data | 700 million user profiles | Data exposure without hacking |
What’s interesting here is that most of these cases were not about highly sophisticated hacking techniques. They were caused by poor system configurations, weak monitoring, and missed updates. This understanding makes prevention very real, and very achievable.
Conclusion
Data breach prevention isn’t about fear, it's about awareness and smart systems. You don’t need to become a cybersecurity expert. But you do need to follow some key principles:
- understand your data and its vulnerabilities
- build strong, consistent habits
- use the right professional tools
- train your team
- stay consistent.
Most importantly, always keep in mind that anything can happen, even in a small business. Because prevention always feels unnecessary until the moment you realize you actually need it. If you take one thing from this guide, let it be this: ‘Small, consistent actions matter more than perfect systems.’
FAQ
The most common causes include weak or reused passwords, phishing attacks, human error, unpatched software vulnerabilities, poor system configuration.
The average cost varies, but globally it is often estimated in the millions of dollars. For small businesses, even a smaller breach can be financially devastating due to legal costs, loss of customer trust and reputation
A data breach usually involves unauthorized access by an external attacker. A data leak often happens due to internal mistakes, such as misconfigured databases, accidental exposure, and human error.
Yes, many cyber insurance policies cover legal fees, customer notifications, and incident response costs. However, coverage depends on the policy and often requires basic security measures to be in place.
It can take months to detect a data breach. That’s a long time, that’s why monitoring systems and alerts are so important. They help reduce detection time and limit potential damage.